CyberespionageCybersecurity
Understanding Cyber Collateral Damage
International LawLaws of War
Proxy War Ethics
International LawInternational Security
Understanding the Challenge of Legal Interoperability in Coalition Operations
International LawLaws of War
Assessing US Justifications for Using Force in Response to Syria’s Chemical Attacks: An International Law Perspective
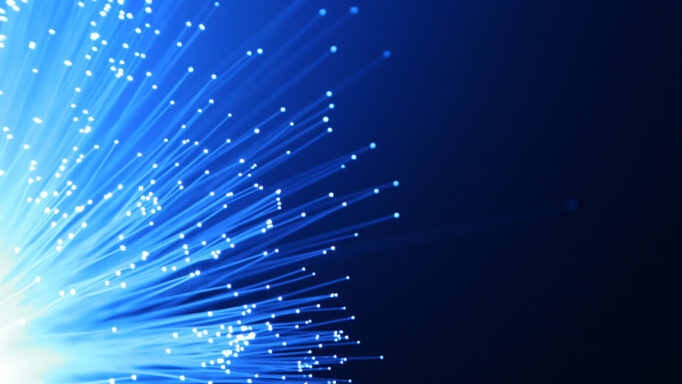
Human RightsPublic Health
Global Health Security in an Era of Explosive Pandemic Potential
Laws of WarTerrorism and Counterterrorism
The Covert Action Statute: The CIA’s Blank Check?
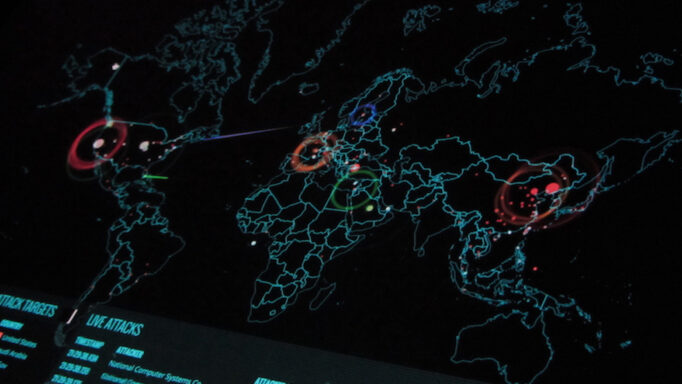
CyberespionageCybersecurity
The 2014 Sony Hack and the Role of International Law
Human Rights in Cyberspace
How Technology Enhances the Right to Privacy: A Case Study on the Right to Hide Project of the Hungarian Civil Liberties Union
Human Rights in Cyberspace
State Responsibility to Respect, Protect, & Fulfill Human Rights Obligations in Cyberspace
CyberespionageCybersecurity
Spying & Fighting in Cyberspace: What is Which?
FISATerrorism and Counterterrorism
Sentencing Considerations & Their Implications on Foreign Policy
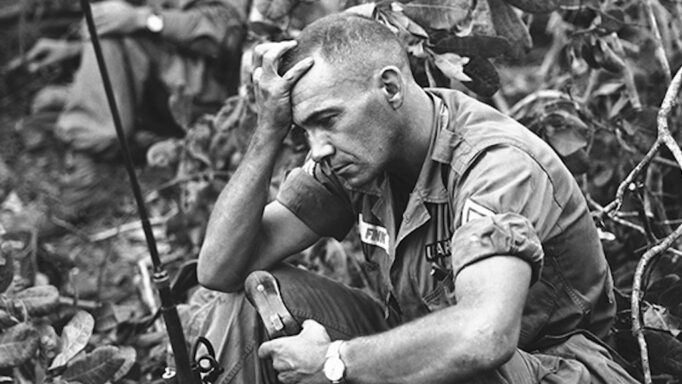
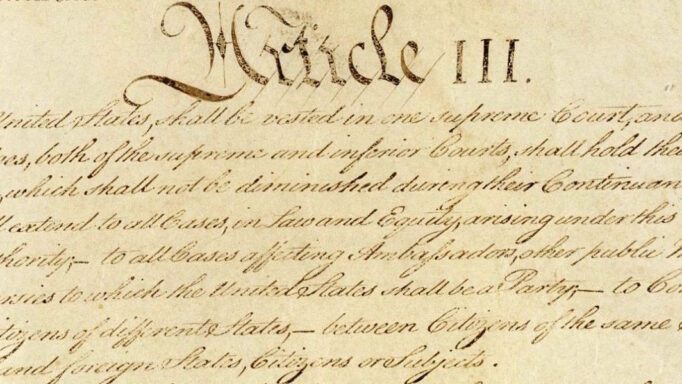
Laws of WarTerrorism and Counterterrorism
The Implications of Trying National Security Cases in Article III Courts
Laws of WarRemote Targeting/Targeted Killing
Dawn of the Intercontinental Sniper: The Drone’s Cascading Contribution to the Modern Battlefield’s Complexity
Laws of WarThe Constitution
No Place in the Military: The Judiciary’s Failure to Compensate Victims of Military Sexual Assault & a Suggested Path Forward Using Lessons from the Prison Context
Laws of WarRemote Targeting/Targeted Killing
“Friend of Humans”: An Argument for Developing Autonomous Weapons Systems
Teaching National Security LawThe Constitution
The National Security Council Legal Adviser: Crafting Legal Positions on Matters of War & Peace