CybersecurityEmerging Technology
A Multiverse of Metaverses
CybersecurityReligious Extremism
Social Media—A Tool for Terror?
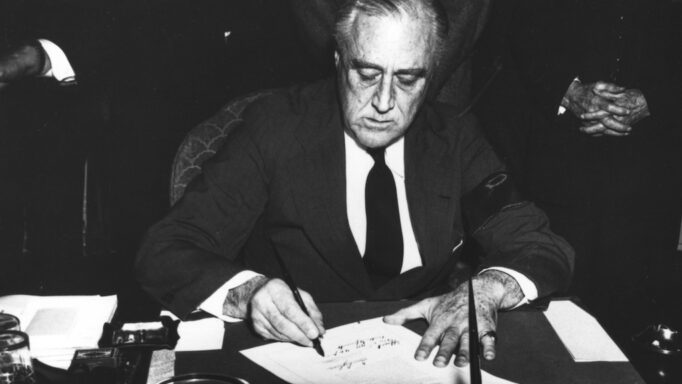
Foreign PolicyInternational Security
FDI Like You’re FDR: CFIUS Review Under the Biden Administration’s Rooseveltian Conception of National Security
Defense PolicyForeign Policy
By, With, And Through: Section 1202 and the Future of Unconventional Warfare
Terrorism and Counterterrorism
“Outside Experts”: Expertise and the Counterterrorism Industry in Social Media Content Moderation
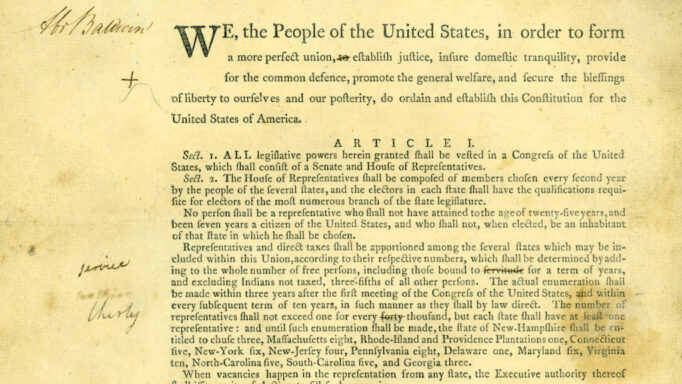
Laws of WarThe Constitution
The Selling of a Precedent: The Past as Constraint on Congressional War Powers?
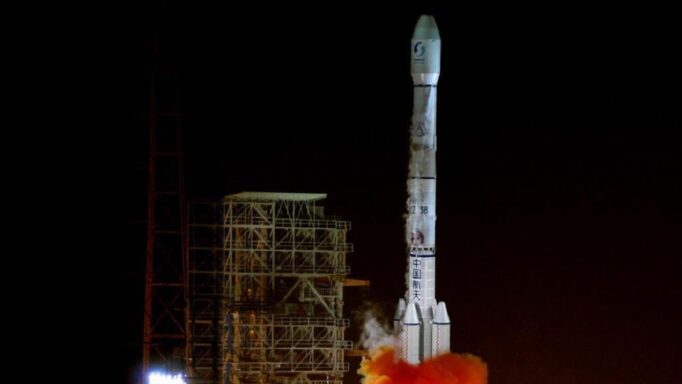
Law and Security in Space
Olive Branches or Fig Leaves: A Cooperation Dilemma for Great Power Competition in Space
CyberespionageCybersecurity
Active Cyber Measures: Reviving Cold War Debunking and Deterrence Strategy
Refugees and ImmigrationTerrorism and Counterterrorism
Turning US Vetting Capabilities and International Information-Sharing to Counter Foreign White Supremacist Terror Threats
Big DataEmerging Technology
Layered Opacity: Criminal Legal Technology Exacerbates Disparate Impact Cycles and Prevents Trust
Foreign PolicyInternational Law
Assessment of National Security Concerns in the Acquisition of U.S. and U.K. Assets
Foreign PolicyIntelligence
Information Lawfare: Messaging and the Moral High Ground
Terrorism and Counterterrorism
Rethinking U.S. Efforts on Counterterrorism: Toward a Sustainable Plan Two Decades After 9/11
Special Online Issue: Capitol Insurrection 2021The Constitution
Introduction to the Special Online Issue on the 2021 Capitol Insurrection
Special Online Issue: Capitol Insurrection 2021The Constitution
The Attack on the Capitol Calls for a Measured Response
Special Online Issue: Capitol Insurrection 2021The Constitution
A Besieged Capitol: The Need to Objectively Assess the Nature of the Violence
Special Online Issue: Capitol Insurrection 2021The Constitution
The Capitol Insurrection and Pineapples on Pizza
Special Online Issue: Capitol Insurrection 2021The Constitution
From 9-11 to January 6: The Limits of Surveillance Authority and the Democratic State
Special Online Issue: Capitol Insurrection 2021The Constitution
Taking Congress and the Capitol Seriously as National Security Institutions
Special Online Issue: Capitol Insurrection 2021The Constitution
The January 6, 2021, Capitol Riots: Resisting Calls for More Terrorism Laws
Special Online Issue: Capitol Insurrection 2021The Constitution
Will Brandenburg Provide Protection for Donald Trump in the Second Impeachment Trial?
Special Online Issue: Capitol Insurrection 2021The Constitution
The Capitol Invasion and the Framing of Political Violence
Special Online Issue: Capitol Insurrection 2021The Constitution
Stepping Back from the Brink?
Special Online Issue: Capitol Insurrection 2021The Constitution
Perception and Reality: The Urgency of Finding and Fixing Extremism and Racial Bias in the Armed Forces
International LawInternational Security
Why Isn’t Outer Space a Global Commons?
Laws of WarTerrorism and Counterterrorism
“Until They Are Effectively Destroyed”: The U.S. Approach on the Temporal Scope of Armed Conflicts with Terrorist Organizations
International LawLaws of War
Fighting in the Unknown: Lawful Measures to Neutralize Subterranean Threats
International LawInternational Security
The Role of Transnational Private Actors in Ukraine International Flight 752 Crash in Iran Under Economic Sanctions Pressure